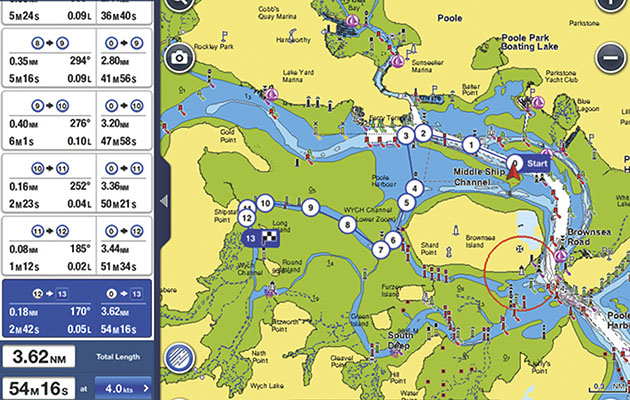
Chartplotters could still be used as standalone devices during the Garmin outage, although charts could not be downloaded
From Yachting Monthly by Katy Stickland
July's Garmin outage left Navionics customers unable to access online services including downloading charts.
We talk to the cyber security firm Red Sky Alliance about the safety of online navigation systems
The Garmin outage in July caused disruption to many of its online services.
The firm was the victim of days-long cyber attack, which began on 23 July.
Navionics customers were unable to access the Navionics server via their log-ins.
The Navionics Boating app, Chart Installer, and Navionics Chart Viewer were all affected; products couldn’t be bought directly via the Navionics website.
The days-long outage meant many Navionics online services couldn’t be used
Charts couldn’t be downloaded, although chart plotters using Navionics software could still be operated as a standalone device.
Garmin has said it had ‘no indication that any customer data was accessed, lost or stolen‘.
Jonathon Sweeney is a program manager with Red Sky Alliance, a cyber security partner of UK maritime security firm Dryad Global.
He spoke to Yachting Monthly about the safety of online navigation systems, and the steps sailors can take to protect themselves from a cyber attack.
Q. In light of the recent Garmin outage, how vulnerable is online navigation to a cyber-attack?
I cannot think of any online service that is NOT vulnerable to a cyber-attack.
Even devices that are ‘air-gapped’ (intentionally disconnected from a network for security) can be vulnerable to cyber-attacks.
GPS is made up of three parts – receivers, satellites, and ground stations.
Any one of these parts is vulnerable to an attack.
For example, if an attacker can tamper with a GPS receiver on a cell phone, they can trick the device into thinking it is in a different location, even if the satellites and ground stations are unaffected.
This would likely affect an individual user.
If an attacker is able to successfully activate ransomware on the systems which keep the ground station operating, that would likely interfere with GPS capabilities for multiple users, unless there are redundant ground stations available.
With the increase in Operational Technology (OT – hardware and software that detects or causes a change through the direct monitoring and/or control of physical devices, processes and events) and Internet of Things (IoT) technologies (the network of physical objects—“things”—that are embedded with sensors, software, and other technologies for the purpose of connecting and exchanging data with other devices and systems over the internet) and the increase in connected devices, these systems will only become more vulnerable.
Q. How vulnerable is the GPS network to attack, such as GPS spoofing?
This is not something ‘some teen in the basement’ is likely to target.
While it is possible, hacking a GPS network does require a relatively high skill level.
As demonstrated by University of Texas at Austin students in 2013, GPS spoofing can be done by overpowering the signals coming from satellites and replacing them with the attacker’s signal.
As we saw in the Garmin outage, it was a WastedLocker attack believed to be from a sophisticated group known as EvilCorp, not just some random person who got lucky.
The biggest vulnerability in this chain of systems is in the receiver.
Hacking a satellite and/or ground systems is possible, but targeting the receiver is much easier, and much less likely to raise intrusion alarms.
Q. How likely are the above scenarios?
In short, not likely.
There have been proofs of concept, but attackers do not seem to target these systems.
This is because there are other simpler/easier ways of earning a profit or damaging a company.
As targeting these systems becomes easier, attacks will become much more likely.
The highest likelihood scenario would be a hostile country spoofing a ship’s GPS to trick that ship into wandering into restricted territory.
They could then seize that ship for political, financial, or other reasons, by claiming it entered their waters illegally.
Or another scenario is where attackers target a ship with innocent civilians and interferes with GPS for notoriety/profit.
Again, the more companies which rely on connected systems for their GPS, the higher the likelihood of an attacker taking advantage of them.
Q. Is enough being done by the public and private sector to mitigate the threat of attack on online navigation networks?
No.
Neither the public nor the private sector are doing enough to mitigate the threat to navigation systems.
If history is any indicator, it will take a much more significant event than the Garmin outage to trigger change in this field.
If a cruise ship were to be stranded in the middle of the ocean without any navigation systems because of a cyber-attack, that may trigger people to pay more attention.
But with everything going on in the world, many companies and public agencies are already strained.
If Garmin and others in the public sector were doing enough to secure their systems, there may still have been a cyber-attack, but the damage would not have resulted in an outage, let alone the Garmin outage which lasted days.
This is where having redundancy and backups comes into play (LORAN-C to eLORAN), but that costs time, money, and other resources are strained.
Governments are also not doing enough to go after attackers.
Groups like EvilCorp have been so successful because they are able to remain safe in their countries and they can commit attacks knowing that they are not going to be prosecuted or punished.
There is not nearly enough pressure on these safe-harbour countries to hand these attackers over to the proper authorities.
As with all aspects of navigation, following ‘best practice’ is the surest way to make sure you are passage planning…
Most of us navigate using MFDs, phones and tablets, or even drones.
But can electronic backups be a substitute for…
Q. Should recreational sailors be concerned about the threat of a cyber-attack and its impact on online navigation?
At this time, I would not be concerned as a skilled recreational sailor.
First of all, they are much less likely to be targeted because an attacker would not gain much from attacking an individual (unless the person is rich and/or famous).
Also, if a recreational sailor becomes stranded, they can call the Coast Guard or other public service to assist them.
If an attacker targets a Coast Guard vessel’s GPS, it becomes a much more complex situation.
Lastly, recreational sailors should already know how to operate their vessels if all electronics should fail, making them less appealing targets.
Q. How might a recreational sailor recognise that their online navigation has been compromised?
The short answer is that a recreational sailor probably would not know until it is too late (i.e.
they have reached the incorrect destination).
The problem with spoofing a receiver, is that the receiver ‘thinks’ it is still working properly so it may never display an alarm indicating something is wrong.
Things to look for include:
Systems operating abnormally (providing unusual data, making abnormal noises, displaying security alerts, etc.)
On-screen navigation is not matching up with visual navigation (Vessel path looks incorrect).
Damage to systems (hardware overheating, applications/software is not loading, etc.)
A ‘good’ sailor would always have navigation charts, a cell phone and a VHF radio on board their recreational vessel.
Q. What steps can recreational sailors take to mitigate against this?
The biggest step is to learn to navigate offline.
Use traditional navigation techniques (map and compass, celestial, etc.)
If a sailor can navigate without online systems, an attack becomes significantly less damaging.
Making sure you can navigate traditionally, without electronics, will help protect you from a cyber attack.
Credit: Graham Snook/YM
Purchase systems from vendors that have implemented some level of security in their systems.
Pay attention and be aware of common threats to these types of systems.
They are not a big target right now, but again, that is likely to change in the future.
Keep ALL online systems up to date with the newest updates and software patches.
This is often difficult for non-technical people, but many attackers take advantage of vulnerabilities that have been public for years.
Q. Can online navigation ever be really secure?
Secure? Yes.
Impregnable? No.
Nothing that is ‘online’ is ever invincible to cyber-attack, but there are ways to secure communications between the three systems, such as strong encryption.
Also removing default passwords on any navigation systems is a requirement.
Creating redundant backup systems and non-digital fail safes as often as possible is also critical.
Ironically, one way many companies are securing themselves is to pay someone to break into these systems and then tell the company how to prevent an attacker from doing the same (a.k.a.
a penetration test).
Links :
- Yachting Monthly : Smart Navigation: From paper charts to augmented reality


No comments:
Post a Comment